Welcome to another Hack the Box Walkthrough. In this blog post, I have documented how I owned the Sea machine on Hack The Box. Hack The Box is a cybersecurity platform that helps you bridge knowledge gaps and prepares you for cyber security jobs.
About the Machine
The Sea machine on Hack The Box (HTB) is an easy-difficulty challenge. Initial access can be gained by exploiting a vulnerability, such as CVE-2023–41425, to obtain a reverse shell. Another approach involves exploiting WonderCMS, cracking a password hash, and then escalating privileges. Sea is an Easy Difficulty Linux machine that features CVE-2023-41425 in WonderCMS, a cross-site scripting (XSS) vulnerability that can be used to upload a malicious module, allowing access to the system. The privilege escalation features extracting and cracking a password from WonderCMS's database file, then exploiting a command injection in custom-built system monitoring software, giving us root access.
This writeup detailed how I pwned the Sea machine on Hack the Box. The first step in solving this machine is to connect the Kali Linux terminal with the Hack the Box server. To do this, I logged in to my Hack the Box account and click the “connect to HTB” button. I chose EU servers and click on the “Download VPN” button.
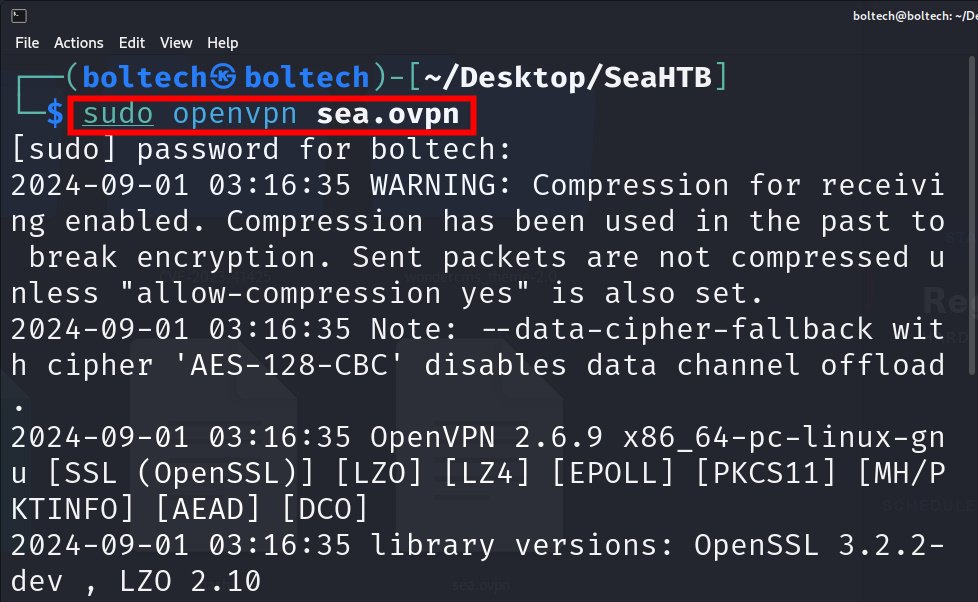
Once the lab access file has been downloaded, I renamed it to sea.ovpn and moved it into a new folder I have created on my desktop called “SeaHTB”. Once the file had been moved, I opened the directory in my terminal by right-clicking and chose the option “Open in terminal." Once my terminal had been opened, I typed the following commands to establish a connection between my Kali Linux terminal and Hack the Box server:
The sudo openvpn sea.ovpn command connected my Kali Linux terminal and Hack the Box server together. Once the connection has been successfully established, I performed Nmap enumeration to scan for open ports that are available on the target machine. This step is crucial to know what the machine is all about and what the next step to perform is.
I right-clicked on the terminal and chose “split terminal vertically” to open a new terminal. Then, I typed the following command to find the open ports on the target machine IP address:
I found two open ports after scanning with Nmap. The ports are 22/tcp and port 80/tcp. Looking at port 80/tcp, it is clear the machine is a web application because it contains Apache hhtpd header, and it also has the “PHPSESSID” and http-title: Sea - Home header.
Once all these processes have been completed, the next step was adding the IP address of the machine into the etc/hosts file on my Kali Linux terminal. There are multiple ways to do this, for simplicity, I went with the easiest method of using the sudo command. To add the IP address, I typed the following command on the Kali Linux terminal:
The command launched the GNU interface, then I added the IP address in the following format (as shown in the picture below)
Alternatively, you can use
echo “10.10.11.28 sea.htb” | tee -a /etc/hosts
After I have added the IP address, I navigated to the Firefox browser and visited “10.10.11.28.” this redirected me to the official website of Sea Machine.
The website basically has two navigation buttons, “home” and “how to participate.” The home tab contains an introductory message about the website and the company. I didn’t find anything interesting there, so I clicked the bottom “how to participate” and found the tab contains a link titled “contact” where the participant can forward their data such as their name, email, age, and country.
This is getting interesting because I can actually write a cross-site scripting code to take over the system if the user inputs are not sanitized and validated.
I tried writing some cross-site scripting injection code, but none of it worked. After carefully observing the official website of Sea, I noticed the text “Velik71” on the main page, so I decided to check Google to find out about it. Luckily, I came across the WonderCMS website, which gave me a detailed explanation of what the text means. Velik71 is actually a template used on the WonderCMS platform, which serves as a template for bike lovers and those who want to diversify their website. The Velik71 was built using WonderCMS technology.
After I had figured this out, the next step was searching for WonderCMS vulnerabilities by using Google search, and luckily, I stumbled upon the CVE-2023-41425.
The CVE-2023–41425 is a cross-site scripting vulnerability in WonderCMS v3.2.0 through v.3.4.2, which allows a remote attacker to execute arbitrary code via a crafted script uploaded to the install module component.
How the CVE-2023–41425 works
To run the attack, a Python file “exploit.py” must be created to perform the following action.
- Imitating the attacker: I used the following three arguments to perform the attack (URL, IP address, and Port number). The URL points to where the WonderCMS is installed, the IP address of the attacker’s machine, and the attacker’s machine port.
- Generating an xss.js file: The exploit.py generates an xss.js file for reflected XSS and outputs a malicious link.
- Opening/Clicking the file: Once the admin (logged user) opens the malicious link, a background request is made without the admin's acknowledgment to upload a shell via the upload theme/plugin functionality.
- Uploading the shell: After uploading the shell, I gained a reverse connection to the server.
Performing the exploit
I clicked on the code button on the GitHub page of prodigiousMind/CVE-2023–41425 GitHub repository.
and clicked on the copy URL to clipboard icon to copy the link.

After that, I navigated back to the SeaHTB directory on my desktop, opened my terminal there, and cloned the GitHub repository by typing the following commands:
Once the cloning has been completed, I ran the ifconfig command to find the IP address of my host machine by running the following command:
Looking back at the Nmap scan result, I found two open ports. Port 22/TCP, which is associated with SSH service (that means I need to get a reverse shell connection/secure encryption to this port.) I navigated into the CVE-2023–41425 directory and found two files downloaded (exploit.py) and (ReadME.md) inside the directory. Next, I opened the directory in my Kali Linux terminal and ran the following command to listen to the incoming connection at port 4444:
While listening at port 4444, I opened a new terminal and ran the exploit.py file against the port to obtain the reverse shell by running the following command:
According to the documentation on the GitHub page, running the command above might not work until you trigger it by running the curl command. To trigger the exploit, I ran the following command in the terminal:
After running the curl command, I obtained the shell. To keep the shell active, I needed to stabilize it by running the following:
Once the shell had been stabilized, I listed all the files in the directory by running the ls command on my terminal. I found the following directories:
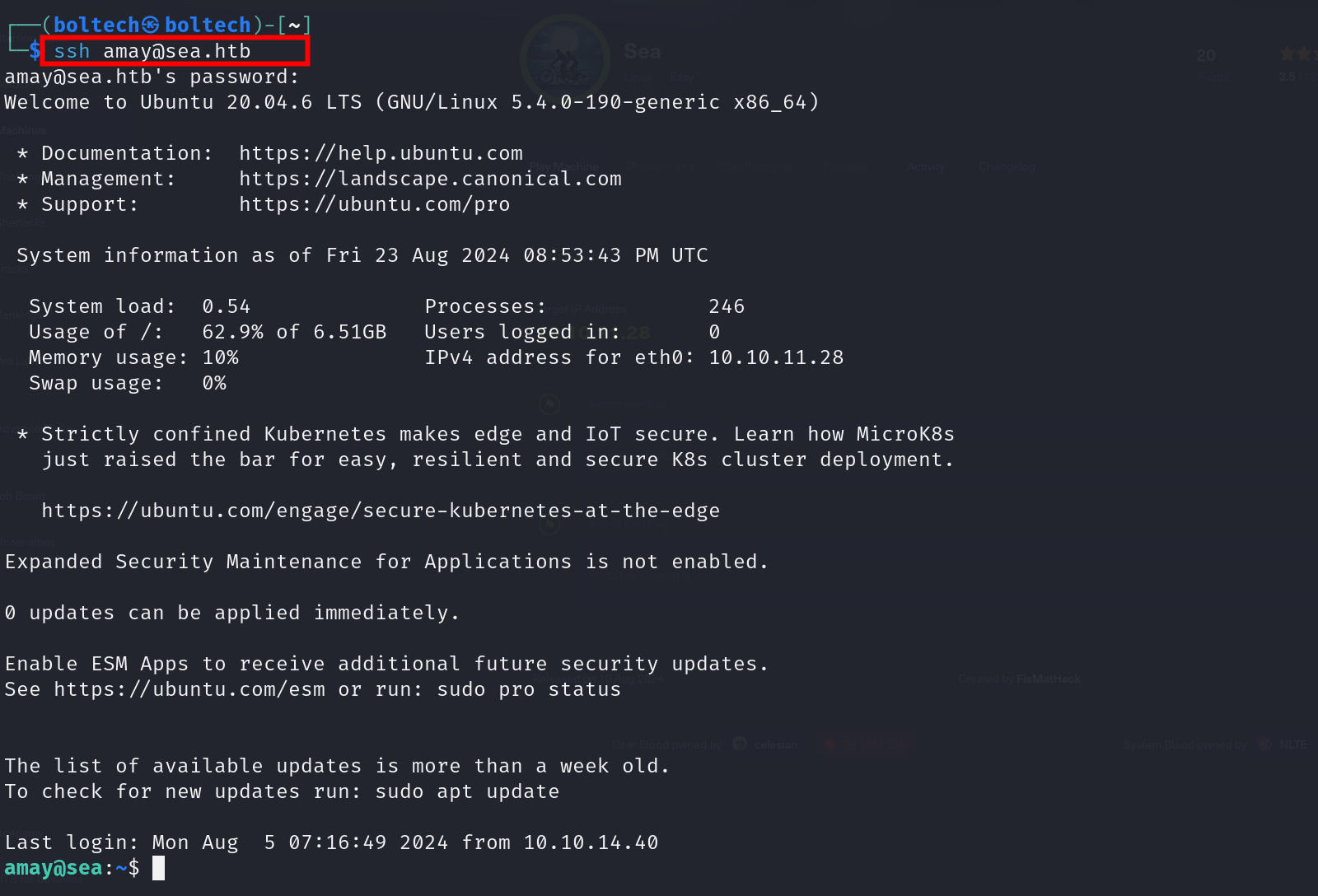
I found the home directory among the list of directories, so I navigated into it by changing my directory with the cd /home command. Afterward, I listed all the files again using the ls command, and I found two directories, “amay” and “geo.” Next, I moved into the directory by running the following command:
ls amay
Inside the amay directory, I found the user flag and attempted reading it using the cat user.txt command but failed!!! The permission was denied. Unfortunately, I couldn’t read the file and needed another method. So, I checked up on other vulnerabilities associated with WonderCMS, hoping to find another way around it.
Some screenshots and description’s are still missing. I will provide them later…
Next, I listed all the files in the directory by running the ls command and found the user.txt flag. To read the content of the user flag, I ran the following command in my terminal:
cat user.txt
This walkthrough was first published on Medium on September 19th 2024 but was pulled down by Hack the Box for violating its policy. The walkthrough had 408 views and 186 reads on Medium.
Keywords:
eighteen htb writeup
eighteen htb walkthrough
eighteen htb
htb eighteen writeup
eighteen writeup
hackthebox eighteen writeup
htb eighteen walkthrough
eighteen walkthrough
eighteen writeup htb
htb eighteen
gavel htb
eighteen hack the box
eighteen hackthebox writeup
eighteen hackthebox
hack the box eighteen
gavel htb writeup
eighteen walkthrough htb
gavel writeup
htb gavel writeup
eighteen.htb writeup
hackthebox eighteen walkthrough
eighteen hack the box walkthrough
hack the box eighteen walkthrough
hackthebox eighteen
eighteen.htb
eighteen htb machine
"eighteen.htb"
eighteen write up
htb gavel walkthrough
eighteen htb write up
eighteen hackthebox walkthrough
hack the box eighteen writeup
"eighteen" hackthebox writeup
hackthebox gavel writeup
htb eighteen write up
eighteen machine htb
dc01.eighteen.htb
"eighteen" htb writeup
eighteen hack the box writeup
htb gavel
htb "eighteen" writeup
gavel hackthebox writeup
eighteen.htb walkthrough
gavel htb write up
"eighteen" htb walkthrough
htb "eighteen"
htb signed
gavel htb walkthrough
gavel.htb
"overwatch.htb"
gavel hack the box
gavel walkthrough
eighteen writeup hackthebox
signed htb
gavel writeup htb
writeup eighteen
hackthebox "eighteen"
"eighteen.htb" writeup
gavel hackthebox walkthrough
signed.htb
"giveback" htb writeup
"monitorsfour"
htb gavel sql injection payload inventory.php
htb gavel walkthrough sql injection payload inventory.php
hack the box gavel sql injection payload inventory.php
overwatch htb writeup
hack the box gavel sql injection payload inventory.php 2025
htb machine editor xwiki simplistcode pro
htb gavel walkthrough sql injection inventory.php
hack the box gavel walkthrough sql injection payload inventory.php
htb gavel walkthrough sql injection inventory.php payload
hack the box gavel walkthrough sql injection payload
htb gavel sql injection payload inventory.php sort
"gavel.htb"
nanocorp htb
hack the box gavel sql injection payload 2025
gavel.htb/admin.php
htb gavel walkthrough pdo injection sort parameter
htb gavel walkthrough sql injection payload
nanocorp walkthrough
eighteen.htb:5985
gavel 2.0 exploit
"0673ad90a0b4afb19d662336f0fce3a9edd0b7b19193717be28ce4d66c887133" password
gavel.htb/includes
hercules htb writeup
nanocorp htb writeup
editor htb
gavel-util
overwatch htb walkthrough
"hack the box" "eighteen" writeup
hack the box gavel walkthrough pdo injection
htb overwatch writeup
signed htb walkthrough
"eighteen" htb
hercules htb walkthrough
guardian htb writeup
hackthebox overwatch writeup
htb eighteen admin password iloveyou1
gavel.htb/rules
editor htb walkthrough
hercules htb
gavel hackthebox
nanocorp writeup
overwatch writeup htb
conversor htb walkthrough
htb monitorsfour
htb overwatch walkthrough
hackthebox hercules
"dc01.eighteen.htb"
ina2we6harj2gaw!
hackthebox "eighteen" writeup
"browsed.htb"
monitorsfour.htb:5985
overwatch.htb:5985
htb eighteen machine walkthrough
"eighteen" hack the box writeup
eighteen htb github
gavel writeup hackthebox
gavel.htb/.git
hack the box eighteen machine walkthrough
giveback walkthrough
hackthebox gavel walkthrough
hackthebox gavel
htb editor writeup
overwatch hack the box writeup
"overwatch" htb writeup
nanocorp htb walkthrough
overwatch hackthebox writeup
overwatch.htb writeup
hackthebox nanocorp writeup
overwatch writeup hackthebox
giveback htb writeup
htb nanocorp writeup
"browsed" htb writeup
htb topology writeup
htb browsed
"0673ad90a0b4afb19d662336f0fce3a9edd0b7b19193717be28ce4d66c887133"
signed walkthrough
htb gavel write up
"giveback.htb"
htb 18
giveback htb
htb guardian writeup
hercules writeup
wiki.editor.htb
monitorsfour.htb/robots.txt
monitorsfour htb writeup
pterodactyl hack the box walkthrough
editor.htb
conversor walkthrough
htb edit
hack the box eighteen machine
giveback htb walkthrough
htb hercules writeup
pterodactyl htb walkthrough
planning htb
monitorsfour htb walkthrough
hackthebox monitorsfour
htb nanocorp
pterodactyl htb writeup
pterodactyl writeup htb
pterodactyl hackthebox walkthrough
artificial htb
hackthebox pterodactyl
pterodactyl hackthebox writeup
htb pterodactyl writeup
browsed htb writeup
hackthebox nanocorp
htb planning
browsed walkthrough
facts htb walkthrough
htb facts writeup
pingpong htb write up
logging htb write up
silentium htb write up
variatype htb write up
cctv htb write up
facts htb write up
eloquia htb write up
fries htb write up
nanocorp htb write up
hercules htb write up
cobblestone htb write up
interpreter htb write up
wingdata htb write up
pterodactyl htb write up
eighteen htb write up
garfield htb write up
devarea htb write up
kobold htb write up
pirate htb write up
monitorsfour htb write up
overwatch htb write up
hack the box season 10 machine walkthrough
hack the box season 10 machine write up
hack the box season 10 machine complete solution
hack the box season 10 machine root flag
hack the box season 10 machine user flag





























0 Comments